OAuth 2.0 JWE access token enforcement - API Policy
home
Enforces use of signed and encrypted JWT access tokens within an authorization header to access the API on which the policy is applied. This policy decrypts the JWE using shared AES key, then validates signature by using provided URL with RSA JWK key set and finally verifies JWT claims: iss, exp, nbf. The JWK Set is cached for period of 10 minutes to prevent delays.
If any of this fails, the policy rejects access to the API and returns 401 Unauthorized status code.
Supported Encryption Algorithms
- AES_128/GCM/NoPadding (A128GCM in JWT terminology)
- AES_256/GCM/NoPadding (A256GCM in JWT terminology)
Supported Signature Algorithms
- SHA256withRSA (RS256 in JWT terminology)
- SHA384withRSA (RS384 in JWT terminology)
- SHA512withRSA (RS512 in JWT terminology)
Required Token Properties
HTTP Authorization header must have the following form: Bearer <token>
The token consist of 5 Base64url encoded fields concatenated with "dot" : header.key.iv.ciphertext.tag
- header - Contains info about JWE.
- key - Is empty, because direct content encryption is assumed.
- iv - Initialization vector for encryption algorithm (usually random bytes).
- ciphertext - Encrypted JWS in compact serialization (header.payload.signature).
- tag - Authentication tag. Product of authenticated encryption.
JWE Header Fields
JWE header fields must be as follows:
- alg
dir - cty
JWT - enc
A128GCMorA256GCM
Example JWE header:
{
"alg" : "dir",
"enc" : "A128GCM",
"cty" : "JWT"
}Nested JWS Header Fields
Nested JWS header fields must be as follows:
- alg
RS256orRS384orRS512 - typ
JWT
Example JWS header:
{
"alg": "RS256",
"typ": "JWT"
}JWT Claims
The following JWT claims are validated:
- iss - must match the provided required issuer
- exp - expiration time must be in the future. This must be present in JWT.
- nbf - not before - if provided in JWT, it must be in the past.
Example JWT claims:
{
"sub": "12345",
"nbf": 1479124625,
"iss": "https://issuer.example.com",
"exp": 1481716745,
"iat": 1479124745,
"ssn": "13245-324-543"
}Configuration
The policy configuration contains several input parameters:
- Issuer - defines an issuer of JWT token. It is usually in URI/URL form.
- JWKs URL - URL pointing to the JSON Web Key Set containing RSA public keys.
- Signature algorithm - Algorithm to use to verify signature of nested JWS
- Encryption algorithm - Algorithm to use to decrypt the JWE
- Encryption key - Base64 URL encoded AES key. If the AES key is in JWK form, it is the value of the 'k' key.
Example Configuration:
- Issuer
https://issuer.example.com - JWKS URL
https://issuer.example.com/oauth2/keys.jwks - Signature algorithm
RS256 - Encryption algorithm
A128GCM - Encryption key
dHLyjIik981jQZ1nafdMJc
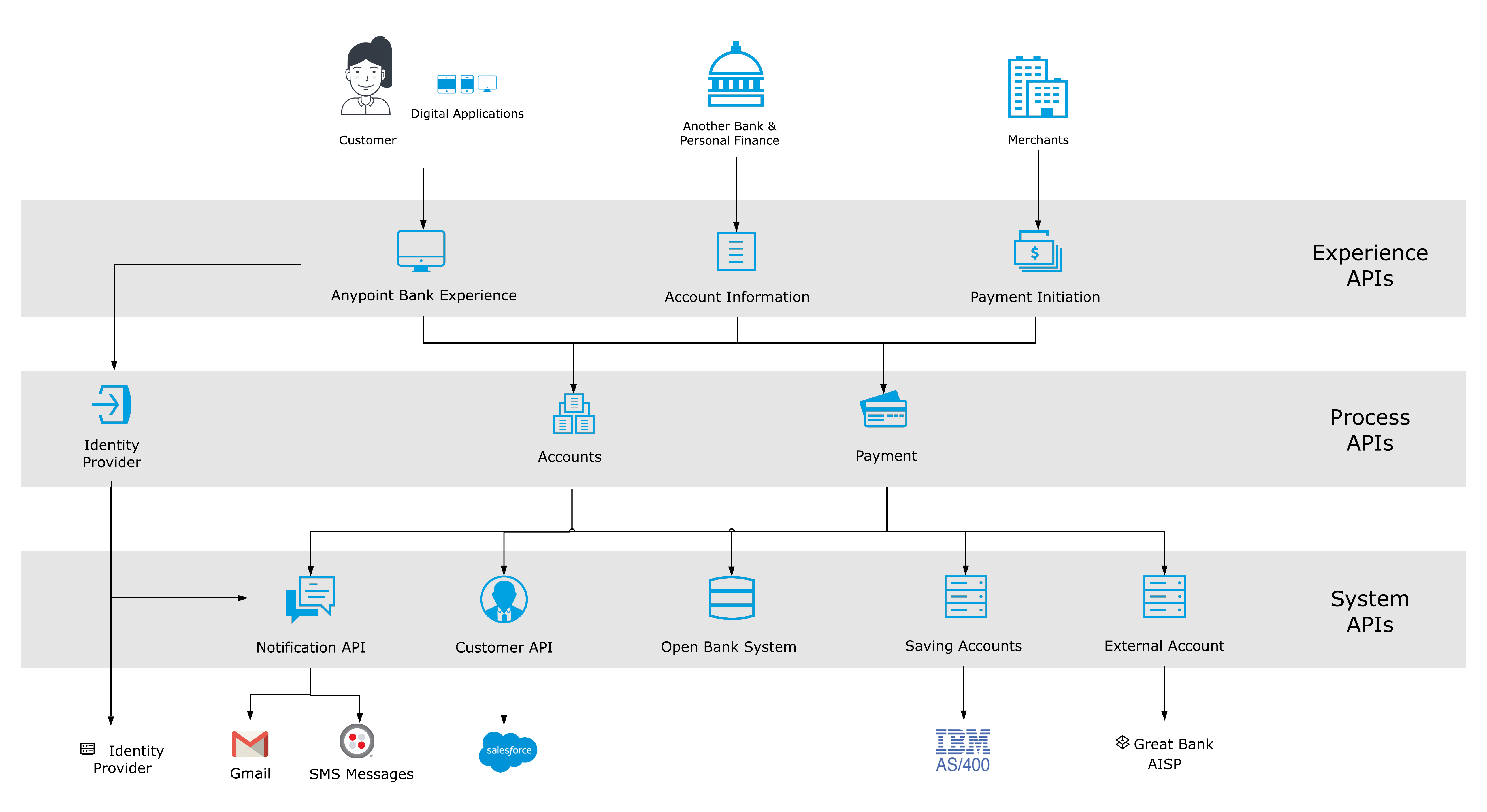
Catalyst Accelerator for Banking
This API implementation is one of many components included in Catalyst Accelerator for Banking. It provides organizations with connectivity assets that accelerate project delivery in financial services, including pre-built API designs and implementations that support core banking business processes. Please contact mailto info@mulesoft.com to find out more.