OAuth2 Authorization Code Using the HTTP Connector
home
Often you are faced with a requirement to handle authorization to a third party service. This example application illustrates how to execute this type of authorization using the Mule Runtime.
Prerequisites
This document assumes that you are familiar with OAuth, HTTP, Mule, Anypoint connectors, Anypoint Studio, elements in a Mule flow, and global elements.
To follow the steps in this example, you must have a box.com account, which you can create for free if you don't already have one.
You also need Java installed on your computer and admin rights to your computer.
Example Use Case
In this example, a user browses to an HTTPS endpoint, in this case, a user to access data from the Box service. For this purpose, OAuth authorization is triggered. The user is asked to supply their user name and password. If successful, the user clicks a button to be granted access.
Registering an App in the Box Developer Portal
The following steps are only needed in this example so that you can test your finished application.
- Go to Box's developer portal: developers.box.com
- If you do not have an account, create one. If you have one, click My apps in the upper-right corner of the page.
- Click Create a Box Application in the panel on the right. Give it any name, such as MyProxy, then select the Box Content API.
- Click Configure Your Application.
- Look for the client_id and the client_secret. Copy these to a safe place, as you need them later.
- Add a redirect_url. For the purpose of this exercise, set it to https://localhost:8081/callback.
If you're using HTTPS as the Box API requires, you must create a keystore to certify the communication. This can be done using the keytool provided by Java, found in the bin directory of your Java installation. Navigate to this directory on your machine using the command line (this is not needed if Java bin directory is contained in your PATH variable), then execute the following command to create a keystore file:
keytool -genkey -alias replserver -keyalg RSA -keystore keystore.jksThe keytool prompts you to create two passwords. Remember these and fill them in the configuration later on (parameters: keystore.password, keystore.keyPassword). The command creates a .jks file in the directory called keystore.jks.
The keystore (keystore.jks) file along with its corresponding passwords can now be used. Move it into the /src/main/resources directory in Mule Studio's Package Explorer. If you need more help doing this, use this resource.
Building the Example in Studio
- Open oauth2-authorization-code-using-the-http-connector.xml in Anypoint Studio and go to Global Elements. Inside TLS Context element replace the values for keystore keyPassword, keystore password with the corresponding data you entered while creating a keystore using the commandline - see the previous section.
- Go to HTTP Request Configuration element and open the Authentication tab. Fill in the client_id and client_secret you got in the previous section.
- Deploy your Mule Project to the embedded Mule server by right-clicking the project in the Package Explorer, then selecting Run As > Mule Application.
- In any Web browser, enter the following URL: https://localhost:8081/web
- Box prompts you to log in with your username and password. Click Authorize. You can use your personal credentials or create a new test account.
- Clicking Grant access to Box (or Deny access to Box as well) redirects you to http://localhost:8081/callback
- Try the following to perform search call to the Box: https://localhost:8081/web/loginDone
- This example consumes a resource using the recently obtained token (in this case, search for items containing the term "mule") and display the result.
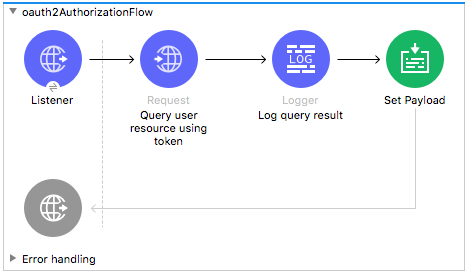
How the OAuth2 Authorization Flow Works
The flow contains two important blocks to showcase OAuth2 dance, HTTP listener and HTTP Request components. First one is an inbound HTTPS endpoint accepts incoming HTTPS GET requests. When request pointing to local authorization URL https://localhost:8081/web arrives, it redirects the processing to Box that basically triggers the OAuth authorization. After the successful operation, the client is redirected back defined as external callback URL in request authentication configuration.
The OAuth authorization is defined by the authorization-code-grant-type component which is wrapped in the HTTP request config component. The request URL is set to https://api.box.com. As HTTPS protocol is specified, TLS context needed to be introduced. The context has three required values: a path, a key password, and a password.
To start an OAuth operation you need a clientId, a client secret issued by the third party service, and a redirect URL that is used after the finished authorization process. To demonstrate some capabilities of this component, custom URL parameters (that is, box_device_id and box_device_name).
After a user is authorized, it is possible to read resources from Box using the recently obtained token, showing the result in the browser.