neuron Document Experience API
Authentication
This page offers comprehensive information on securing access to the API and guides users on viewing their credentials. The content is organized into three main sections:
- Overview: It provides a brief description of the security scheme employed by the API.
- JWT Validation: Steps on how to access the API using JWT token using Oauth2.0.
- Client ID Enforcement: Steps on how to access the API using Client ID Enforcement
Overview
To ensure that the end-to-end service retains appropriate levels of security. This section provides you with information on how the API is secured and explains how to obtain the necessary token to interact with it.
The Insurer Experience API accepts HTTPS/ TLS connections only in order to protect the integrity and confidentiality of any data transferred. HTTP connections are refused and plain text communication is not supported.
As a further means to secure requests, this API uses the following API security methods by default.
Ports
Outbound access to port 443 (HTTPS) is required to connect to Neuron endpoints. This must be considered if traffic traverses the network.
Components, such as firewalls or proxies, may require configuration changes to open ports and enable communication with the Neuron service.
TLS - SSL
For the security of connections to the API, Neuron only accepts TLS 1.2 or higher SSL connections. HTTP connections are refused, and plain text communication is not supported.
Authentication and Authorization
JWT Validation
Using Bearer Token Authorization header
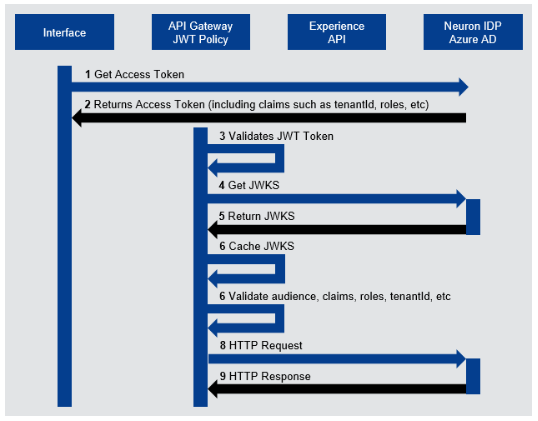
The following provides an overview of the security measures implemented to safeguard access to the API, ensuring data protection, integrity, and confidentiality.
- Azure Active Directory (Azure AD) Integration: Neuron uses Azure AD using the Multi-tenant Application Model to manage user authentication.
- OAuth 2.0: OAuth 2.0 access token enforcement, JWT Validation Policy.
- JSON Web Tokens (JWT): Compact and self-contained tokens that carry claims about the entity. They can be signed using a secret or a public/private key. For added security:
- Audience (AUD) Claim: Validates the recipient of the JWT, ensuring it's intended for the Neuron back-end.
- Expiration (exp) Claim: Tokens have a short lifespan of 60 minutes, ensuring they cannot be misused after a certain period, even if intercepted.
- Roles: Ensure the legitimacy of assigned roles, contributing to a more secure authentication process.
In case of an invalid token, a 401 HTTP Status Code with code Invalid Token will be returned.
Below is an example of how a client application should retrieve and send JWT along with the request to the Insurer Experience API.
Client ID Enforcement
Once you have access to a the client_id, pass the client_id value in the headers as key client_id.
In case of an invalid token, a 401 HTTP Status Code with code Invalid Client Id will be returned.
Accessing JWT Credentials
Neuron Operations and Support team can provide access to JWT.
- Contact details to be followed.